How Multitenant Database Containers Improve Cybersecurity in Modern Enterprise Systems
Multitenant database containers have become a critical architecture in modern database management systems. They allow multiple isolated databases to run within a single shared instance, optimizing resources and simplifying management. This innovative approach is used by major systems like SAP HANA multitenant database containers and Oracle’s PDB architecture. By understanding how this system works, we’ll also explore its cybersecurity benefits and how it helps enterprises scale securely.
What is Multitenancy?
In simple terms, multitenancy refers to a model where a single instance of a software application serves multiple tenants. Each tenant is isolated, ensuring that their data remains secure and private from others. In the world of databases, this model allows multiple databases to share the same resources while remaining independent in terms of user data, schemas, and configurations.
You might also come across terms like multi tenant facility and multi tenant cloud when discussing this architecture. These terms refer to physical and cloud-based environments where multiple tenants (or customers) share resources in an isolated manner, but without compromising security or performance. Multi tenant cloud is particularly relevant in today’s IT landscape, where businesses move their operations to the cloud for flexibility and scalability.
RELATED: Security Vulnerability Assessment: Definition, Process, Tools, and Real Examples
How Multitenant Database Containers Work
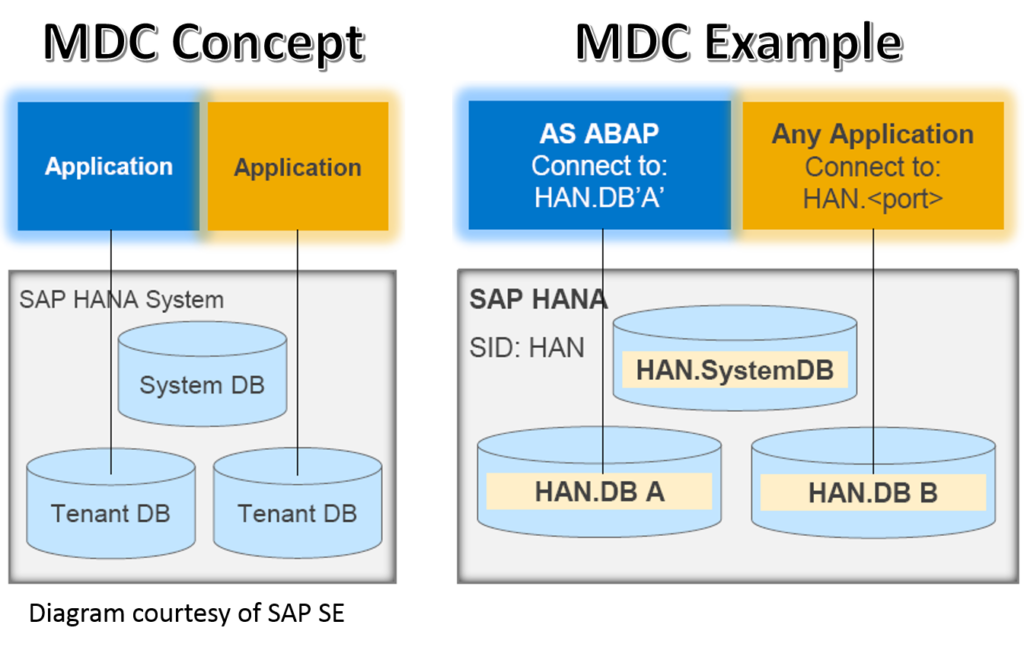
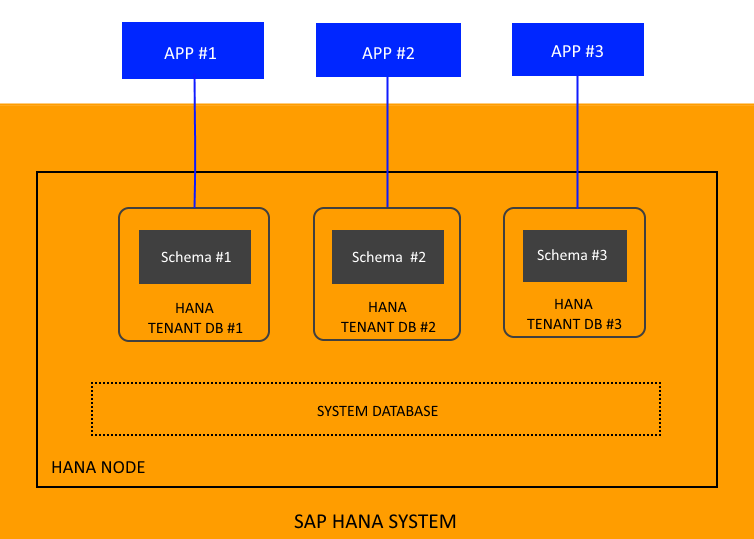
Multitenant database containers are designed to enable multiple independent databases to run within a single container, each functioning like a separate database while sharing the same underlying infrastructure. This architecture provides a balance between resource efficiency and strong isolation, making it ideal for modern enterprises with multiple applications and tenants.
Container Databases and Pluggable Databases (PDBs)
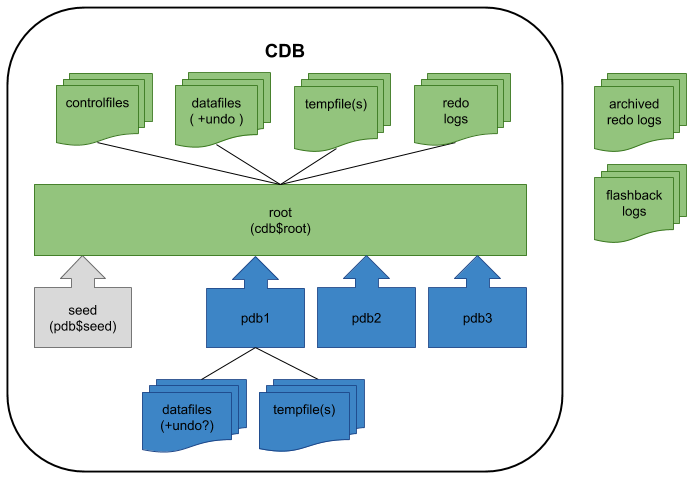
At the core of multitenant database containers is the Container Database (CDB) and its Pluggable Databases (PDBs). The CDB acts as the parent database, containing the shared infrastructure such as memory, processes, and system metadata. On the other hand, PDBs are independent databases that plug into the CDB, each with its own user data, schemas, and metadata.
This separation allows for greater flexibility and isolation between different databases, ensuring that one PDB’s issues, whether in terms of performance or security, do not affect others.
For example, SAP HANA multitenant database containers and Oracle PDB use this architecture to separate different tenants’ databases in a single container database, allowing for more efficient use of resources and easier management.
Key Components of Multitenant Architecture:
- Container Database (CDB): The central database that holds shared resources for all PDBs. It stores common metadata, background processes, and manages resources for all connected PDBs.
- Pluggable Databases (PDBs): These are the individual databases that plug into the CDB. They are self-contained and can be easily created, cloned, or moved.
- Root Container (CDB$ROOT): The root of the CDB, which stores metadata and manages user information common to all PDBs.
How This Enhances Security
By keeping the system and user-level data separate, multitenant databases offer enhanced security and better control over data. This is particularly important for businesses with stringent compliance and data privacy needs. Hana multitenant database containers and similar models allow each PDB to operate independently, even though they share the same infrastructure.
READ MORE: Cloud Security Tips: How to Safeguard Your Data in 2026
The Cybersecurity Benefits of Multitenancy
Multitenant database containers provide more than just operational efficiency, they also offer significant cybersecurity advantages, making them an ideal choice for businesses concerned about data protection, isolation, and compliance. Let’s explore how multitenancy enhances security at different levels of the database architecture.
Improved Security with Isolation
One of the most significant benefits of multitenancy is data isolation. Each Pluggable Database (PDB) operates independently within the Container Database (CDB), which means that data and applications in one PDB remain isolated from others. This isolation is critical for organizations handling sensitive information, such as financial institutions or healthcare providers.
For example, in a multi tenant data center, where multiple applications or organizations share the same physical infrastructure, the ability to isolate each tenant’s database at the PDB level ensures that data breaches or performance issues in one tenant’s environment don’t spill over into others. This isolation also helps businesses comply with industry regulations, such as HIPAA in healthcare or PCI DSS in finance, where strict data privacy and protection measures are required.
Enhanced Security Controls
Another key advantage of multitenant containers is the ability to implement fine-grained security policies. Security can be applied at the PDB level, ensuring that each tenant has its own authentication, encryption, and access control mechanisms. This flexibility allows businesses to enforce role-based access control (RBAC) and tailor security settings for each tenant, improving overall database security.
Additionally, multi tenant cloud environments enable the use of automated security measures, such as continuous monitoring and threat detection, to protect the infrastructure. For instance, cloud computing multi tenant architecture can integrate AI-powered security solutions that identify vulnerabilities, unauthorized access attempts, or unusual activity across multiple PDBs in real time.
Multi-Tenant Application Architecture and Security
In multi tenant application architecture, where a single application serves multiple customers (tenants), multitenant databases enhance security by ensuring that each customer’s data is isolated from others. Whether in a multi tenant facility or a multi tenant deployment, this approach ensures that an attack targeting one tenant doesn’t impact others.
For example, businesses can isolate databases for different clients (tenants) in multi tenant deployment models, enhancing security by preventing cross-tenant data leakage.
Common Challenges in Multitenancy: What Happens When It’s Not Set Up Properly
While the benefits of multitenant database containers are clear, misconfigurations or improper setup can lead to significant challenges, particularly in terms of security and resource management. It’s crucial that organizations understand what can go wrong if multitenancy isn’t configured properly.
Risks of Misconfigurations
When multitenant containers are not set up properly, the isolation between Pluggable Databases (PDBs) can break down, resulting in:
- Data leakage between tenants, where one tenant’s data is unintentionally exposed to another.
- Security vulnerabilities, especially if authentication and encryption are not implemented at the PDB level.
- Resource contention where one tenant’s workload can negatively affect the performance of other tenants sharing the same Container Database (CDB).
In a multi tenant deployment, such issues can lead to downtime and performance degradation across all tenants, impacting business operations. For example, in a multi tenant cloud environment, improperly configured security policies or resource allocation could lead to a breach or loss of sensitive data.
Understanding Multi-Tenant Mismanagement
When systems like SAP HANA multitenant database containers or Oracle’s PDB are not configured correctly, there can be cascading failures. For instance:
- Improper patch management: Patching the CDB might inadvertently affect all PDBs, causing unintended downtime or performance issues.
- Misaligned security settings: A failure to configure access controls properly at the PDB level can open the door to unauthorized access and breaches.
Without proper setup, multi tenant data sources can be compromised, which may lead to legal consequences in regulated industries such as finance and healthcare.
What Happens in a Misconfigured Multi-Tenant Building
Think of a multi tenant building where tenants share common spaces (e.g., parking lots, elevators). If the security system isn’t set up properly, allowing access to restricted areas, it could result in serious security breaches. The same applies to multitenant databases, where improper configuration can expose confidential data and impact other tenants within the same container.
SEE ALSO: Can You Learn Cybersecurity on Your Own (2026)
Securing Your Multitenant Database Containers: Best Practices for Enterprises
To maximize the security and efficiency of multitenant database containers, organizations need to follow best practices that ensure proper configuration, isolation, and resource management. These practices are essential for preventing security breaches, performance issues, and other challenges associated with multitenancy.
1. Plan Resource Allocation Carefully
Proper resource allocation is crucial in a multi tenant data center or multi tenant cloud environment. Container databases and pluggable databases share infrastructure, which means resource allocation must be carefully managed to prevent one tenant from consuming excessive resources at the expense of others.
- Define clear limits for CPU, memory, and I/O for each PDB to avoid resource contention.
- Use resource quotas to ensure that no single PDB overwhelms the system, especially during peak times.
2. Enforce Strong Security Policies at the PDB Level
Each PDB in a multitenant container should have dedicated security settings to maintain strict isolation. Here are some key practices:
- Authentication: Use role-based access control (RBAC) to ensure that only authorized users can access specific PDBs.
- Encryption: Apply encryption at both the PDB and CDB levels to protect sensitive data from unauthorized access.
- Audit Logging: Implement audit logs to track user activity and detect any suspicious behavior.
By enforcing these security measures, you can safeguard each tenant’s data and comply with regulatory requirements like GDPR or PCI DSS.
3. Regular Backup Strategy
Backups should be configured for both the CDB and PDB levels. This ensures that data can be recovered quickly in case of failure, and it helps meet disaster recovery requirements.
- CDB-level backups: Backup shared system data and metadata that applies to all PDBs.
- PDB-level backups: Ensure each tenant’s database is backed up independently to avoid loss of data due to container failures.
4. Monitor Proactively
It’s essential to monitor performance and security across all PDBs to ensure they’re operating smoothly and securely. Use advanced monitoring tools to track:
- Resource usage (CPU, memory, disk I/O)
- Security events (failed login attempts, unauthorized access)
- Performance metrics (query times, response rates)
Proactive monitoring helps detect issues before they escalate, ensuring minimal disruption for tenants.
5. Train Database Administrators
Training your DBAs on the nuances of managing multitenant databases is critical. DBAs should be familiar with:
- The relationship between CDBs and PDBs
- How to apply security policies and manage resources
- How to perform backups and disaster recovery for multitenant containers
MORE: Management System Compliance: CMS Update for 2026
The Future of Cybersecurity in Multitenant Database Architectures
As technology continues to evolve, so too does the multitenant database architecture. With the rise of cloud computing, AI, and edge computing, businesses must adapt to these changes to maintain a secure and efficient database system. Let’s explore the future of multitenant database containers and how cybersecurity will play a central role in their continued growth and success.
Integration with Cloud Computing
The future of multitenant database containers lies in deeper cloud integration. Cloud computing multi tenant architecture will enable enterprises to scale rapidly, deploy new tenants quickly, and improve security with minimal downtime. As more businesses move to the cloud, multi tenant data centers will allow for more cost-effective management, enabling businesses to maximize their infrastructure investment while maintaining the security of each PDB.
For example, a multi tenant deployment on the cloud will enable organizations to scale new applications or services seamlessly, without compromising data security or performance. Security controls in the cloud will evolve, using AI-driven solutions to monitor access patterns and automatically adjust defenses based on real-time data.
AI and Automation in Multitenant Database Security
Artificial intelligence and machine learning are already transforming how we approach cybersecurity, and they will continue to shape multitenant container databases. Future multitenant containers will likely incorporate autonomous security features, such as:
- Self-healing: Automatically detecting and correcting security vulnerabilities or performance issues.
- Predictive analytics: Using AI to predict potential threats based on historical data and trends.
- Automated scaling and patching: Automatically adjusting resources and applying updates to PDBs without manual intervention, reducing human error and improving security.
These innovations will enhance cybersecurity by proactively addressing threats, providing more robust defense mechanisms for each tenant database.
Edge Computing and Multitenant Architecture
As edge computing becomes more prevalent, multitenant databases will be required to handle decentralized data management. In industries like IoT and real-time data analytics, businesses will rely on multi tenant architecture examples that facilitate data processing closer to where it’s generated. Multitenant containers will support these applications by allowing organizations to efficiently manage multiple databases across distributed environments.
Security will remain a top concern at the edge. Each tenant will need isolated environments to prevent breaches, and multitenancy with fastapy will become increasingly important to provide real-time, secure data processing.
Enhanced Security Models
As multitenant database containers evolve, the security models will become more granular and sophisticated. Advanced encryption methods, machine learning-based anomaly detection, and enhanced authentication protocols will all contribute to better isolation and data protection. Organizations will be able to implement role-based security within each PDB to ensure that even within a shared environment, each tenant has appropriate access to their data.
Conclusion
As we’ve explored, multitenant database containers offer a transformative approach to database management, combining security, efficiency, and scalability in one architecture. Whether you’re managing databases for a multi tenant facility or deploying applications on cloud computing multi tenant architecture, the benefits are clear: reduced overhead, improved security, and faster provisioning.
Key Takeaways
- Multitenant database containers enable multiple isolated databases to run within a single container, optimizing resource usage while maintaining strong isolation and security.
- SAP HANA multitenant database containers and Oracle PDB offer businesses a more efficient way to manage multiple databases without sacrificing performance.
- With proper configuration, these containers can provide significant cybersecurity benefits, especially in sectors like finance, healthcare, and logistics, where data isolation is critical.
- As businesses move towards cloud deployment and edge computing, multitenant deployment models will be essential for supporting scalable, secure, and efficient database environments.
- AI-driven automation and enhanced security models will continue to shape the future of multitenant architecture, providing even more robust protection against cyber threats.
The growing adoption of multi tenant cloud and multi tenant data centers signals a future where multitenant database containers become the standard for enterprise systems. By leveraging multi tenant deployment strategies and continuously improving security at every layer, businesses can stay ahead of the curve and ensure their data remains secure in an increasingly interconnected world.
Ready to turn your cybersecurity knowledge into a high-paying career?
At ExcelMindCyber Institute, our 90-day program gives you hands-on experience in risk management, threat detection, and security operations—skills employers are actively hiring for.
If you’re serious about securing a top cybersecurity role, start your journey now.
FAQ
What are the 4 types of database?
The four main types of databases are:
Relational Databases (RDBMS): Organize data into tables with rows and columns. Examples: MySQL, PostgreSQL, Oracle Database.
NoSQL Databases: Designed for unstructured data, offering flexibility for large-scale applications. Examples: MongoDB, Cassandra.
In-memory Databases: Store data in RAM for fast data retrieval. Examples: Redis, SAP HANA.
Graph Databases: Use graph structures with nodes and edges to represent data. Examples: Neo4j, Amazon Neptune.
What are the 5 main data types in databases?
The five primary data types commonly used in databases are:
Integer: For whole numbers (e.g., 1, 100, -23).
Varchar: Variable-length strings (e.g., “John Doe”).
Date/Time: For date and time information (e.g., “2023-05-01”).
Boolean: Represents true/false values (e.g., true, false).
Decimal/Float: For numbers with fractional parts (e.g., 10.5, 3.14).
What is the difference between single tenant and multi-tenant database?
A single-tenant database architecture supports only one tenant or customer per instance, meaning each customer has their own dedicated resources (e.g., CPU, memory, storage). This offers better data isolation but can lead to higher costs and resource inefficiency.
In contrast, a multi-tenant database architecture allows multiple tenants to share a single database instance, with each tenant’s data isolated from others. This is more resource-efficient and cost-effective, especially in cloud environments, but requires careful management to ensure security and performance across tenants.
Is Gmail multi-tenant?
Yes, Gmail is a multi-tenant application. Multiple users (tenants) share the same infrastructure and resources, but their emails, data, and accounts are isolated from one another. Each user’s data is private and protected, ensuring that activities in one account do not affect others.