Security Vulnerability Assessment: Definition, Process, Tools, and Real Examples
A security vulnerability assessment is the process of finding, analyzing, and fixing weaknesses in systems, networks, and applications before attackers exploit them. It uses structured methods and vulnerability assessment tools to detect issues like misconfigurations, outdated software, and security gaps.
In simple terms, a cybersecurity vulnerability assessment helps organizations stay ahead of threats by identifying risks early and fixing them before damage occurs.
In this guide, you will learn the vulnerability assessment definition, how the process works, the tools used, and a real vulnerability assessment example you can understand and apply.

What Is a Security Vulnerability Assessment?
A security vulnerability assessment is a structured review of an organization’s digital and physical systems to uncover security weaknesses. It focuses on identifying known vulnerabilities, assigning risk levels, and recommending fixes.
A cyber vulnerability assessment does not exploit systems. It only discovers and evaluates risks so teams can fix them safely.
Think of it like a routine health check. Instead of waiting for a system to fail, you test it regularly to catch problems early.
Organizations use security assessments to monitor:
- Servers and endpoints
- Networks and infrastructure
- Web and mobile applications
- Cloud environments
A strong cyber security vulnerability assessment gives clear visibility into what is exposed and what needs attention.
RELATED: Difference Between Risk Assessment and Risk Management: 2026 Complete Guide
Why Security Vulnerability Assessments Matter in Cybersecurity
Security threats keep evolving. Attackers look for the smallest weakness and use it to gain access.
A proper risk and vulnerability assessment helps organizations:
- Prevent data breaches before they happen
- Reduce attack surfaces across systems
- Maintain compliance with security standards
- Protect sensitive business and customer data
A threat vulnerability assessment also helps teams prioritize what to fix first. Not all vulnerabilities carry the same risk.
For example, an open port may seem minor, but if it exposes critical data, it becomes a high-risk issue.
Types of Vulnerability Scanning You Should Know
Different systems require different types of scans. Understanding the types of vulnerability scanning helps you choose the right approach.
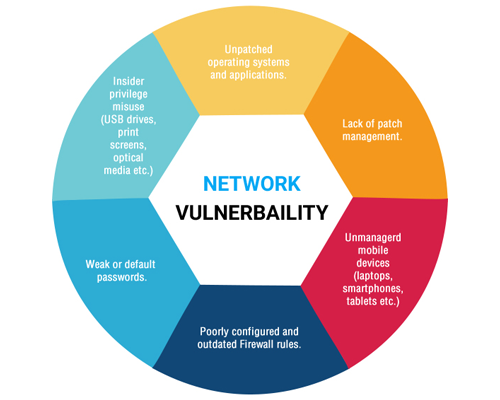
Network Vulnerability Assessment
A network vulnerability assessment focuses on identifying weaknesses in network infrastructure.
It helps with:
- Assessing network security
- Detecting open ports and weak protocols
- Identifying unauthorized access points
Application Vulnerability Assessment
An application vulnerability assessment scans web and mobile applications for security flaws.
It detects:
- SQL injection vulnerabilities
- Cross-site scripting (XSS)
- Weak authentication systems
Host-Based Assessment
This scan focuses on individual systems like servers and workstations.
It checks:
- Patch status
- Configuration issues
- Operating system vulnerabilities
Physical Security Vulnerability Assessment
A physical security vulnerability assessment evaluates real-world security risks.
It looks at:
- Unauthorized physical access
- Surveillance gaps
- Facility entry points
A physical security assessment is important because not all attacks happen online.
READ MORE: What Is a QR Code? Uses, Risks, and Safety Tips
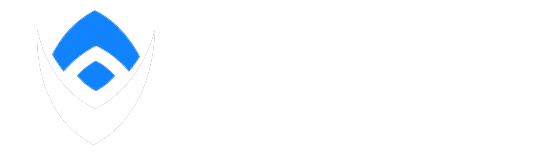
Vulnerability Assessment Methodology (Step-by-Step Process)
A clear vulnerability assessment methodology ensures consistent and accurate results.
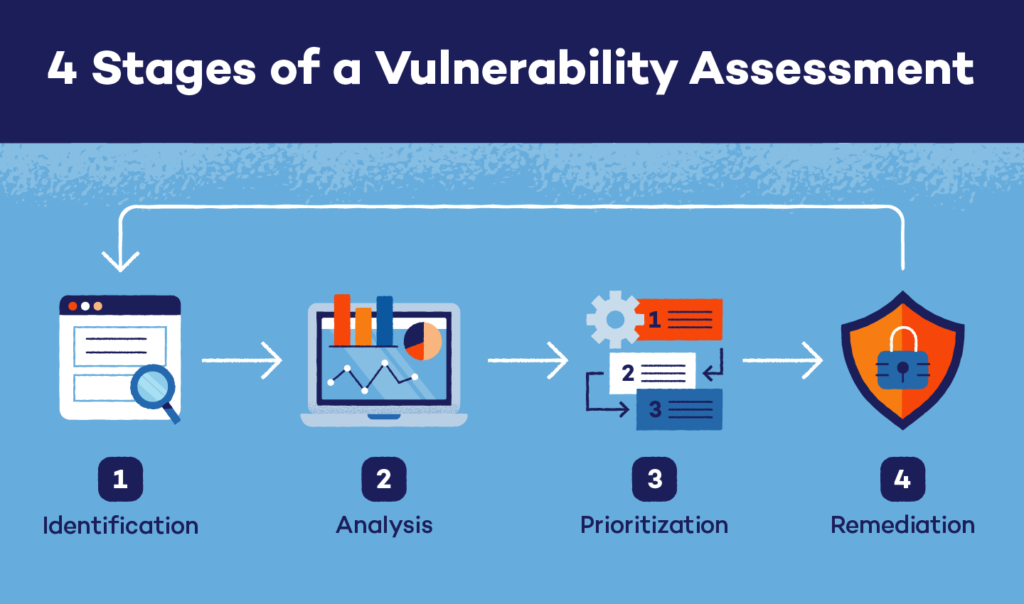
1. Asset Identification
You first identify all systems, devices, and applications in scope.
You cannot protect what you do not know exists.
2. Vulnerability Scanning
You use vulnerability assessment tools in cyber security to scan systems for known weaknesses.
These tools compare systems against databases of known vulnerabilities.
3. Analysis
You analyze the results to understand:
- Root causes
- Affected systems
- Potential attack paths
4. Risk Prioritization
You rank vulnerabilities based on:
- Severity
- Ease of exploitation
- Business impact
This step connects directly to risk and vulnerability assessment.
5. Remediation
You fix the vulnerabilities by:
- Applying patches
- Updating configurations
- Implementing security controls
A strong cyber vulnerability assessment always ends with action, not just reports.
SEE ALSO: Managed Network Services: What Professionals Need to Know in 2026
Best Vulnerability Assessment Tools in Cyber Security
Modern security teams rely on automated tools to scale their efforts.
Common vulnerability assessment tools include:
- Nessus – widely used for network scanning
- Qualys – cloud-based vulnerability management
- OpenVAS – open-source scanning tool
These vulnerability assessment tools in cyber security help teams:
- Scan systems quickly
- Detect known vulnerabilities
- Generate reports for remediation
Each tool focuses on different areas, such as networks, applications, or compliance.
Security Vulnerability Assessment Example (Real Scenario)
Let’s break this down with a real-world vulnerability assessment example.
A fintech company runs a security vulnerability assessment on its customer login portal.
Step 1: Scan the Application
The team uses a vulnerability scanner to test the web application.
The scan reveals that the login form does not properly validate user input.
Step 2: Identify the Vulnerability
The tool flags a potential SQL injection vulnerability.
This means an attacker could enter malicious code into the login form to access the database.
Step 3: Analyze the Risk
The system stores sensitive customer data, including emails and transaction history.
Because the vulnerability sits on a public-facing login page, attackers can easily exploit it.
The risk level is marked as critical.
Step 4: Remediation
The development team fixes the issue by:
- Implementing input validation
- Using parameterized queries
- Updating database security rules
Step 5: Verification
The team runs another scan to confirm the vulnerability no longer exists.
Final Outcome
The company closes a critical security gap before attackers exploit it.
A single overlooked vulnerability could have exposed thousands of customer records.
Key Insight
A cybersecurity vulnerability assessment does not just find problems. It helps teams understand how small weaknesses can lead to major breaches if ignored.
MORE: Operation Per Second: Meaning, FLOPS vs IOPS 2026
Vulnerability Assessment Checklist
Use this vulnerability assessment checklist to stay consistent:
- Identify all assets
- Define scope clearly
- Run vulnerability scans
- Analyze findings
- Rank risks by severity
- Apply remediation steps
- Verify fixes
This checklist ensures no step is missed.
Key Security Vulnerability Assessment Questions to Ask
Strong assessments depend on asking the right questions.
Important security vulnerability assessment questions include:
- What assets are most critical to the business?
- Which vulnerabilities are exploitable right now?
- What data is at risk?
- How severe is the potential impact?
- What is the fastest way to fix this issue?
These questions guide better decision-making.
What a Vulnerability Assessment Report Should Include
A good vulnerability assessment report should be clear and actionable.
It must include:
- Identified vulnerabilities
- Severity levels (e.g., CVSS score)
- Affected systems
- Risk impact
- Recommended fixes
This report helps teams move from detection to remediation.
Vulnerability Assessment vs Penetration Testing
A security vulnerability assessment identifies weaknesses.
A penetration test goes further and exploits those weaknesses.
Key difference:
- Assessment = Find problems
- Pen testing = Prove how attackers can exploit them
Both are important, but they serve different purposes.
Security Vulnerability Assessment Template (Simple Framework)
A simple security vulnerability assessment template should include:
- Scope of assessment
- Tools used
- Identified vulnerabilities
- Risk levels
- Remediation plan
This structure keeps assessments organized and repeatable.
Vulnerability Assessment Services (When to Outsource)
Many organizations use vulnerability assessment services when they lack in-house expertise.
A vulnerability assessment service can help:
- Run advanced scans
- Provide expert analysis
- Deliver detailed reports
Outsourcing ensures accuracy and saves time.
ALSO: What is a TCP/IP Protocol? Networking Importance in 2026
How This Skill Helps You Start a Cybersecurity Career
Understanding cybersecurity vulnerability assessment is a valuable skill.
It opens doors to roles like:
- Security analyst
- GRC analyst
- Risk and compliance specialist
Companies need professionals who can identify and fix vulnerabilities before attacks happen.
Conclusion
A security vulnerability assessment helps organizations find and fix weaknesses before attackers do. It provides a clear path from detection to remediation.
When done consistently, it strengthens security posture, reduces risk, and prepares teams for evolving threats.
Understanding cybersecurity is one thing. Getting paid for it is another.
If you’re serious about breaking into cybersecurity, don’t stop here. Join ExcelMindCyber and start building the skills that lead to high-paying roles.
FAQ
What’s the difference between CVE and CVSS?
CVE (Common Vulnerabilities and Exposures) is a list that identifies and names known security vulnerabilities. Each vulnerability gets a unique CVE ID.
CVSS (Common Vulnerability Scoring System) assigns a severity score to those vulnerabilities. It helps teams understand how dangerous a vulnerability is and how quickly they should fix it.
What are the top 10 vulnerabilities?
The most widely recognized list comes from the OWASP, known as the OWASP Top 10.
It includes common risks like:
– Broken access control
– Cryptographic failures
– Injection attacks (e.g., SQL injection)
– Security misconfigurations
– Vulnerable and outdated components
These vulnerabilities represent the most critical risks in modern web applications.
What are common vulnerability assessment tools?
Common tools used in a cybersecurity vulnerability assessment include:
Nessus – widely used for network scanning
Qualys – supports continuous monitoring
OpenVAS – free and flexible for many environments
These tools automate scanning, identify known vulnerabilities, and generate reports for remediation.
What does CVSS 9.8 mean?
A CVSS score of 9.8 indicates a critical vulnerability.
It means:
– The vulnerability is easy to exploit
– It requires little or no authentication
– It can cause serious damage, such as data breaches or full system compromise
Security teams treat CVSS 9.8 issues as top priority and fix them immediately to reduce risk.