Cybersecurity Internship Technical Interview Questions
Cybersecurity Internship Technical Interview Questions
While other IT fields have faced ups and downs, cybersecurity remains in high demand, even in tough economic times. But where there is demand, there is also competition, and to get a job in Cybersecurity, you need to be one of the best.
While having the necessary Cybersecurity skills is only one side of the equation, acing a cybersecurity interview is another thing altogether. Cybersecurity internships are a critical stepping stone for people looking to enter the rapidly evolving field of cyber defense.
Interviews for cybersecurity internships are designed to test both your theoretical knowledge and your ability to apply it to real-world scenarios. Recruiters often assess foundational concepts, practical problem-solving, and even how well you keep up with industry trends.
In this article, we’ll guide you through common cybersecurity internship technical interview questions, offer tips for freshers, and provide insights into leveraging resources like cybersecurity question PDFs and Reddit communities for preparation.

Start a Life-Changing Career in Cybersecurity Today
READ MORE: Is Cybersecurity Hard to Learn? A Complete Analysis
Cybersecurity Interview Questions: Core Technical Concepts
When preparing for a cybersecurity internship interview, it’s vital to master foundational technical concepts. These form the backbone of most questions and are often explored through theoretical queries and practical applications. Below, you will see an outline with key areas you should focus on, including examples of cybersecurity internship technical interview questions for freshers.
1. Cryptography Basics
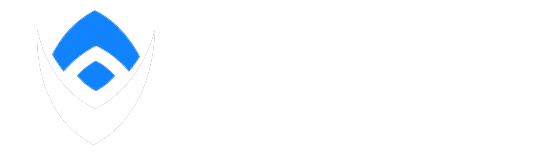
Cryptography is a cornerstone of cybersecurity. Interviewers may test your knowledge of concepts like encryption, hashing, and digital signatures. Examples of common questions include:
- What is the difference between symmetric and asymmetric encryption?
Symmetric encryption uses the same key for encryption and decryption, while asymmetric encryption uses a pair of keys (public and private) for secure communication. - How does hashing ensure data integrity?
Hashing creates a fixed-length string from input data, ensuring that even small changes to the data will result in a different hash.
For an in-depth study, cybersecurity internship technical interview questions PDFs often feature a dedicated section on cryptography.
2. Network Security Essentials
Your understanding of network protocols and their vulnerabilities is crucial. Be ready to address both theory and practical measures to secure networks. Examples include:
- What are the layers of the OSI model, and how does each layer contribute to network security?
The seven layers include Physical, Data Link, Network, Transport, Session, Presentation, and Application. For instance, encryption occurs at the Presentation layer to secure data transmission. - How do you secure a Wi-Fi network?
Implement WPA3 encryption, use strong passwords, and disable WPS to prevent unauthorized access.
Many scenario-based cybersecurity interview questions explore network security breaches, asking candidates how they would react to real-world challenges.
3. Threats and Vulnerabilities
Understanding risks like malware, phishing, and insider threats is essential. Some potential questions include:
- What’s the difference between a vulnerability, a threat, and a risk?
A vulnerability is a weakness in the system, a threat is a potential exploit of that weakness, and a risk is the likelihood of damage resulting from the exploit. - How would you prevent an SQL injection attack?
By using parameterized queries, validating user inputs, and limiting database permissions.
Scenarios like these are frequently discussed in cybersecurity internship technical interview questions Reddit threads, where candidates share their approaches and solutions.
READ MORE: Can You Get a Job with Google Cybersecurity Certificate? Find Out How
Scenario-Based Cybersecurity Internship Technical Interview Questions
Employers often use scenario-based cybersecurity interview questions to assess your ability to apply technical knowledge in real-world situations. These questions are designed to gauge critical thinking, problem-solving skills, and your understanding of cybersecurity best practices.
1. Analyzing Security Incidents
One of the most common scenarios involves analyzing and responding to security breaches. Examples of questions include:
- Example: You notice unusual traffic patterns on the network. How would you identify a compromised system?
Start by analyzing logs for suspicious activities, use intrusion detection systems (IDS) to pinpoint anomalies, and cross-reference findings with threat intelligence databases. - Example: Your organization has been targeted by a phishing campaign. How would you respond?
Educate users to identify phishing attempts, enforce multi-factor authentication (MFA), and block malicious IPs using a firewall.
2. Preventative Measures
Scenario-based cybersecurity interview questions for freshers often test how well you can implement preventative measures. Some examples:
- Example: How would you secure a newly deployed web server?
Start by disabling unused ports, enabling a web application firewall (WAF), and ensuring SSL/TLS encryption is properly configured. - Example: What steps would you take to prevent an MITM (Man-in-the-Middle) attack?
Use encrypted communication protocols like HTTPS, enforce strong authentication methods, and educate users about avoiding insecure Wi-Fi networks.
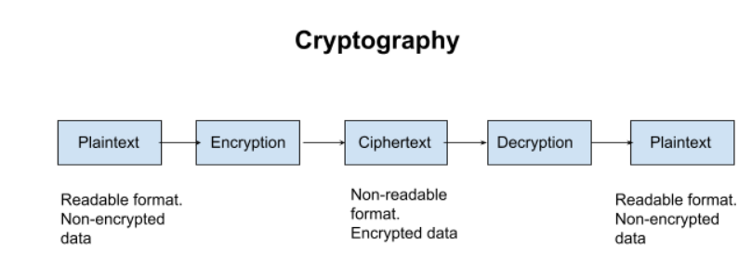
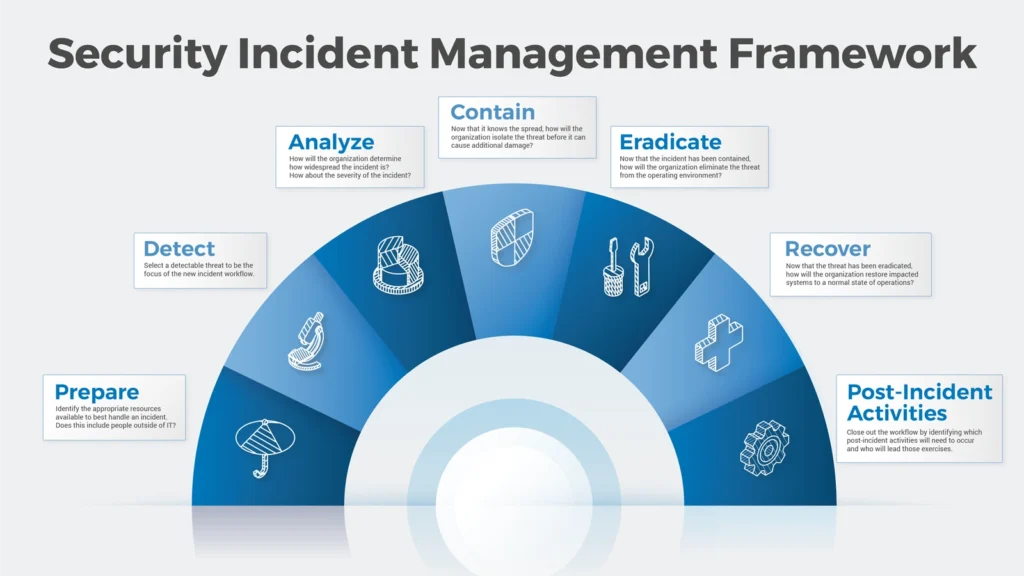
3. Incident Response Planning
Employers may also explore how you would react to critical incidents.
- Example: You’ve identified malware on a company workstation. What’s your response plan?
Immediately isolate the affected system, analyze the malware using sandboxing tools, and scan the network for further infections. Finally, apply patches to prevent reoccurrence. - Example: A stakeholder is putting sensitive data at risk by using weak passwords. How would you handle the situation?
Politely educate the stakeholder about the importance of strong passwords, implement password complexity requirements, and enable two-factor authentication (2FA).
Resources like cybersecurity internship technical interview questions PDFs often include mock scenarios like these to help candidates practice.
Essential Cybersecurity Tools and Techniques

Understanding the tools and techniques commonly used in cybersecurity is crucial for excelling in a technical interview. Employers expect candidates, especially interns, to demonstrate familiarity with industry-standard tools and methodologies. These tools range from basic utilities for monitoring and securing networks to advanced systems for incident response and forensic analysis.
1. Network Monitoring and Analysis Tools
Cybersecurity professionals use monitoring tools to detect and mitigate threats in real-time. Freshers should familiarize themselves with these:
- Wireshark: Learn how to capture and analyze packet data to identify anomalies.
- Splunk: Understand how to use this for centralized logging and threat monitoring.
- Traceroute: Employers may ask, “Do you have experience with Traceroute?” and expect you to explain how it aids in diagnosing network connectivity issues.
2. Security Information and Event Management (SIEM)
SIEM systems consolidate security events from various sources, enabling rapid threat detection. Interns should know the fundamentals of:
- Log correlation.
- Alert tuning to reduce false positives.
- Investigating incidents reported by SIEM tools.
3. Encryption and Hashing Tools
Encryption is the backbone of secure communication. Be prepared to discuss tools and processes like:
- OpenSSL: Used for generating encryption keys and certificates.
- Hashcat: A password-cracking tool that helps test encryption resilience.
Common interview questions include:
- “What is the difference between symmetric and asymmetric encryption?”
- Symmetric uses the same key for encryption and decryption, while asymmetric uses a public-private key pair.
4. Vulnerability Scanning and Penetration Testing Tools
These tools help identify and fix security gaps. Freshers should know how to work with:
- Nmap: For scanning open ports and services.
- Metasploit: For simulating attacks to test system defenses.
Employers may pose questions like:
- “What is a black box penetration test?”
- It involves testing without any prior knowledge of the system, mimicking real-world attack scenarios.
5. Firewall and Endpoint Security Solutions
Interns should understand the basics of setting up and managing firewalls to control network traffic. Techniques include:
- Configuring IP whitelists and blacklists.
- Monitoring traffic for malicious activities.
Expect scenario-based cybersecurity interview questions, such as:
- “How would you set up a firewall to secure a corporate network?”
- Block unused ports, define access control lists (ACLs), and enable intrusion prevention system (IPS) capabilities.
6. Forensics and Malware Analysis Tools
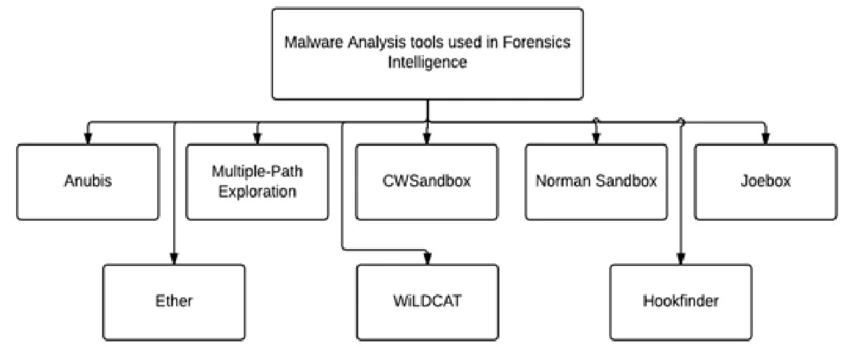
Cybersecurity often involves incident investigation. Freshers should explore tools like:
- Volatility: For memory forensics.
- IDA Pro: For reverse-engineering malware.
Employers might ask:
- “What steps would you take to analyze a ransomware attack?”
- Isolate the affected system, use forensic tools to identify the malware’s entry point, and decrypt data if possible.
RELATED: CompTIA Security Vs Google Cybersecurity Certification
Scenario-Based Cybersecurity Interview Questions
Employers increasingly use scenario-based cybersecurity interview questions to assess a candidate’s ability to apply theoretical knowledge in practical, high-stress situations. These questions evaluate problem-solving, critical thinking, and communication skills—all essential for a successful cybersecurity intern.
1. Identifying and Mitigating Threats in a Network
Example: “A user reports unusual activity in their email account, such as unauthorized password reset requests. What steps would you take to investigate and resolve the issue?”
A good response might include:
- Verifying the user’s account activity through logs.
- Checking for unauthorized login attempts or IP addresses.
- Enforcing multi-factor authentication (MFA) to secure the account.
- Educating the user on phishing risks.
2. Handling a Data Breach Incident
Example: “Your organization discovers a potential data breach affecting customer records. What would you do first?”
Interns should outline a structured approach:
- Immediate containment by isolating affected systems.
- Analyzing the breach to determine its scope and entry point.
- Coordinating with the incident response team to mitigate damage.
- Notifying stakeholders and regulatory bodies, if required.
3. Protecting Against Malware Attacks
Example: “You are notified of a sudden spike in network traffic from a single user, which appears to be exfiltrating data. What is your response?”
Employers expect detailed steps:
- Quarantining the user’s system to stop the data leak.
- Running a malware scan to identify and remove malicious software.
- Checking firewall and SIEM logs for similar activities across the network.
- Updating software and applying patches to prevent further exploitation.
4. Setting Up Security Measures for a New Server
Example: “You are tasked with securing a new server for deployment. What measures would you implement?”
A strong answer includes:
- Configuring strong passwords and removing default credentials.
- Enabling encryption for sensitive data.
- Setting up firewalls and intrusion detection systems (IDS).
- Regularly updating and patching server software.
5. Educating Employees on Cybersecurity Best Practices
Example: “A high-ranking executive refuses to follow company policies regarding password management. How would you handle this?”
Effective strategies include:
- Explaining the potential risks to the company’s reputation and operations.
- Demonstrating real-world examples of breaches caused by weak passwords.
- Offering to help set up secure password management tools.
6. Assessing and Managing Risk
Example: “How would you prioritize fixing multiple vulnerabilities discovered during a security audit?”
Candidates should show prioritization skills:
- Addressing high-risk vulnerabilities that could lead to data loss or service disruptions first.
- Scheduling patches for medium-risk issues during maintenance windows.
- Documenting low-risk vulnerabilities for future improvement.
7. Handling Social Engineering Attacks
Example: “An attacker poses as an IT support team member to gain access to an employee’s account. What actions would you take?”
Interns should focus on:
- Identifying how the attacker gained trust.
- Educating employees on verifying identities before sharing information.
- Enhancing policies to include mandatory identity verification for IT requests.
READ MORE: How to Become a GRC Analyst?
Tips for Preparing and Excelling in a Cybersecurity Internship Interview

Securing a cybersecurity internship involves more than just understanding technical concepts, it requires strategic preparation and effective communication during the interview. Here are some actionable tips to help candidates excel.
1. Understand the Fundamentals of Cybersecurity
Interviewers expect candidates to demonstrate a solid grasp of cybersecurity basics, including:
- The CIA triad (Confidentiality, Integrity, Availability).
- Key differences between encryption, hashing, and encoding.
- Familiarity with common vulnerabilities and attack vectors.
Pro Tip: Study cybersecurity internship technical interview questions PDFs for quick and structured insights into core concepts.
2. Stay Updated on Industry Trends
Cybersecurity is a rapidly evolving field, and staying current can set you apart. Follow cybersecurity blogs, forums, and Reddit communities where industry professionals discuss real-world challenges and solutions. Topics like Zero Trust Architecture and AI in cybersecurity are hot right now.
3. Practice Technical Problem-Solving
Scenario-based questions test how well candidates can apply knowledge in real-world situations. Prepare by:
- Solving cybersecurity puzzles and Capture-The-Flag (CTF) challenges.
- Reviewing common questions in cybersecurity internship technical interview questions and answers PDFs.
4. Polish Your Behavioral Responses
Employers value interpersonal and team collaboration skills. Prepare STAR (Situation, Task, Action, Result) responses for common behavioral questions, such as:
- Handling conflicts within a team.
- Communicating technical problems to non-technical stakeholders.
- Responding to constructive criticism during a project.
5. Highlight Relevant Experience
Even if you’re a newbie, showcase:
- Hands-on projects, such as setting up firewalls or conducting vulnerability scans.
- Any cybersecurity certifications, like CompTIA Security+ or CISSP.
- Participation in cybersecurity competitions or university clubs.
6. Prepare Thoughtful Questions for Interviewers
Asking insightful questions shows enthusiasm and a willingness to learn. Examples include:
- “What tools and technologies does your team primarily use?”
- “How does the company address emerging threats like AI-driven cyberattacks?”
7. Mock Interviews and Resources
Conduct mock interviews with peers or mentors to boost confidence. Leverage resources like cybersecurity questions for students and technical interview guides tailored for freshers.
Pro Tip: Reddit threads often feature firsthand experiences from candidates who’ve succeeded in similar interviews.
8. Stay Calm and Be Honest
If you’re unsure about an answer, it’s better to admit it and explain how you would find a solution rather than guess. Employers value honesty and problem-solving potential over perfection.
SEE MORE: What Coding Language Should I Learn for Cyber Security?
Conclusion
Preparing for a cybersecurity internship interview requires a combination of technical knowledge, problem-solving ability, and interpersonal skills. By understanding the core principles of cybersecurity, practicing scenario-based questions, and leveraging resources like cybersecurity internship technical interview questions PDFs or community forums on Reddit, candidates can gain a significant edge.
Internships serve as a gateway to building a career in this dynamic field, and excelling in interviews ensures a strong start. Focus on continuous learning, stay updated with the latest industry trends, and confidently showcase your skills. With the tips and insights shared, you are well-equipped to tackle any cybersecurity interview challenge and embark on a successful journey in the industry.
FAQ
How do I prepare for a cybersecurity technical interview?
Master the Fundamentals: Review key concepts in networking, operating systems, encryption, and security protocols. Be familiar with common cybersecurity tools and techniques.
Hands-on Practice: Set up a lab environment to practice penetration testing, vulnerability assessments, and network security. Participate in Capture the Flag (CTF) challenges and other online platforms.
Know Common Attack Types: Be prepared to discuss different cyberattacks such as phishing, malware, ransomware, and SQL injection. Understand how to prevent and mitigate these threats.
Study Common Tools: Learn to use tools like Wireshark, Metasploit, Burp Suite, and Nmap. Interviewers often ask about the tools you are familiar with and how to use them.
Review Incident Response Procedures: Be ready to talk about how to handle a security breach or incident, including steps for detection, containment, eradication, and recovery.
Be Prepared to Solve Real-World Problems: You may be asked to solve case studies or given hypothetical scenarios. Focus on demonstrating your critical thinking and problem-solving skills.
Stay Updated: Cybersecurity evolves rapidly. Keep up with recent breaches, emerging technologies (like AI and machine learning in cybersecurity), and regulatory requirements.
What are the 5 C’s of cybersecurity?
The 5 C’s of Cybersecurity are essential principles for securing an organization’s digital assets:
Confidentiality: Ensuring that sensitive information is accessible only to those authorized to view it.
Integrity: Maintaining the accuracy and consistency of data, ensuring that it is not tampered with or altered by unauthorized individuals.
Availability: Ensuring that systems and data are available when needed and protected against disruptions.
Compliance: Adhering to legal, regulatory, and organizational policies to ensure cybersecurity measures meet required standards.
Cybersecurity Awareness: Educating individuals within an organization to recognize threats, follow best practices, and mitigate risks.
What are the 3 C’s of cybersecurity?
The 3 C’s of Cybersecurity typically refer to:
Confidentiality: Protecting sensitive data from unauthorized access or exposure.
Control: Ensuring that security measures are in place to prevent unauthorized actions and control access to systems and information.
Compliance: Adhering to legal and regulatory requirements to ensure that cybersecurity practices align with industry standards and laws.
What are the 5 P’s of cybersecurity?
The 5 P’s of Cybersecurity are often cited as:
Protect: Protecting systems and data from unauthorized access, breaches, or attacks.
Prevent: Preventing security incidents through proactive measures like firewalls, encryption, and access controls.
Predict: Using threat intelligence and analytics to predict and prepare for potential cyber threats.
Prepare: Developing incident response plans, policies, and training to be ready for security incidents.
Pursue: Continuously assessing, updating, and improving cybersecurity strategies to stay ahead of increasing threats.
Transform your career with ExcelMindCyber’s roadmap to six-figure success in cybersecurity. Our program delivers essential guidance and strategies to help you master the skills and secure the roles that matter. Start today and take the first step towards transforming your career!