What is a TCP/IP Protocol? Networking Importance in 2026
TCP/IP (Transmission Control Protocol/Internet Protocol) is the backbone of the internet, enabling seamless communication between computers and devices across networks. Whether you’re browsing the web, sending emails, or streaming content, TCP/IP makes it all possible by breaking data into manageable packets and ensuring their accurate delivery.
For anyone aiming to work in cybersecurity, understanding the TCP/IP protocol is crucial. This knowledge forms the foundation of securing networks, managing communication protocols, and troubleshooting connectivity issues, making it an essential skill for those looking to land a 6-figure cybersecurity job.
What is a TCP/IP Protocol? The TCP/IP protocol is a set of rules that governs how data is exchanged over the internet and private networks. It enables devices to communicate with each other, whether they’re on the same local network or across the globe.
The protocol is made up of two main components: TCP (Transmission Control Protocol) and IP (Internet Protocol). TCP is responsible for breaking data into packets and ensuring these packets are delivered in the correct order, making the data transfer reliable. IP, on the other hand, handles the addressing and routing of these packets to ensure they reach the correct destination.
In essence, TCP/IP allows computers to send, receive, and process data across various network types, from local area networks (LANs) to the vast global internet. This system’s functionality is a cornerstone of modern communication, ensuring the safe and efficient transmission of data between systems.

How Does the TCP/IP Protocol Work?
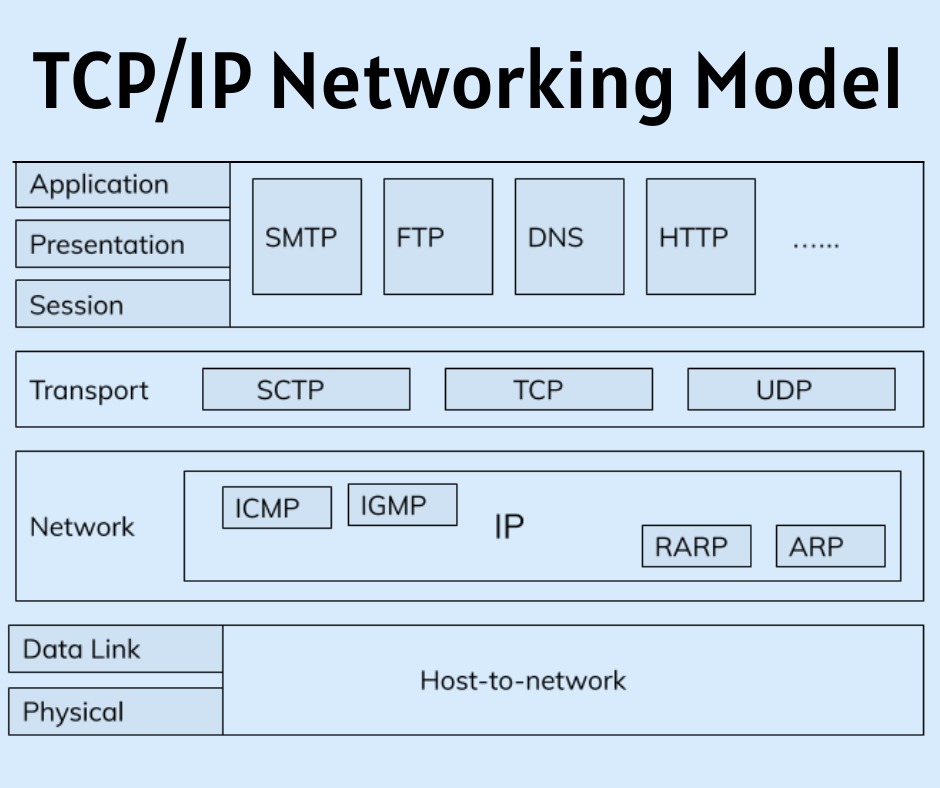
The TCP/IP protocol operates through a four-layer model that breaks down communication tasks to ensure data is transmitted efficiently and reliably. Here’s how it works:
- Breaking Down Data: When data is sent, TCP divides it into smaller packets, adds sequence numbers, and ensures each packet is error-free.
- Routing Data: IP takes these packets and adds the necessary addressing information, determining the best route for each packet to travel across networks.
- Transmission: The data packets are transmitted through various devices, such as routers and switches, until they reach the destination network.
- Reassembly: Once the packets arrive at the destination, TCP reassembles them in the correct order, ensuring the original data is complete and intact.
This process happens almost instantly, enabling seamless communication between devices, whether it’s a simple email or streaming a video.
READ MORE: Why Computer Virus Prevention is Critical for Aspiring Cybersecurity Professionals
Understanding the TCP/IP Model Layers
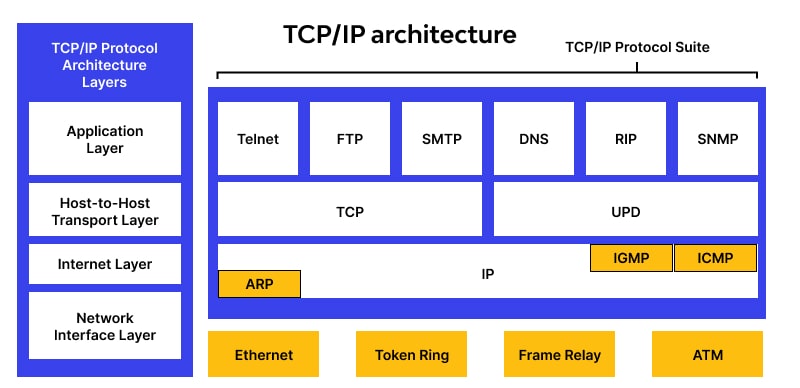
The TCP/IP model consists of four layers, each with specific functions that work together to ensure smooth and reliable data communication. Here’s a breakdown of each layer:
- Application Layer:
This is where all the communication protocols for applications reside. HTTP (for web browsing), SMTP (for email), and FTP (for file transfers) are examples of protocols at this layer. It’s responsible for enabling services that users directly interact with, such as accessing websites or sending emails.
- Transport Layer:
The Transport Layer manages end-to-end communication between systems. TCP operates at this layer, ensuring data packets are delivered reliably. It establishes a connection, breaks down data into smaller packets, and ensures that they are delivered in the correct order. For faster but less reliable communication, UDP (User Datagram Protocol) is used instead.
- Internet Layer:
At the Internet Layer, IP takes charge by handling the addressing and routing of packets to their destination. This layer ensures data travels through the correct network paths and reaches the intended recipient.
- Network Access Layer:
This is where physical transmission happens. It manages the sending and receiving of data over physical devices like Ethernet, Wi-Fi, or fiber optics. It ensures the data is correctly transmitted from one device to another over the network.
SEE ALSO: Cloud Security Tips: How to Safeguard Your Data in 2026
What is the Difference Between TCP and IP?
While TCP (Transmission Control Protocol) and IP (Internet Protocol) work together to ensure seamless communication over networks, they have distinct roles:
- TCP:
TCP ensures reliable delivery of data. It breaks data into smaller packets, assigns them sequence numbers, and ensures they arrive in the correct order. TCP also checks for errors, requests retransmissions if packets are lost, and manages flow control to avoid network congestion. TCP operates at the Transport Layer of the TCP/IP model.
- IP:
IP, on the other hand, is responsible for addressing and routing these data packets. It defines how data is sent from one device to another across networks by using IP addresses. IP operates at the Internet Layer, and it doesn’t guarantee delivery. Its job is simply to ensure the packets reach the correct destination.
Together, TCP handles the reliability and order of data, while IP handles the addressing and routing, making them complementary protocols in the TCP/IP suite.
MORE: Is a Masters in Cybersecurity Worth It in 2026?
TCP/IP in Real-Life Applications
The TCP/IP protocol is essential for a variety of real-life applications that we rely on every day. For instance:
- Web Browsing: When you access a website, HTTP (Hypertext Transfer Protocol) uses TCP/IP to transmit the data packets that load the web page onto your device.
- Email Communication: When sending an email, SMTP (Simple Mail Transfer Protocol) uses TCP/IP to send and receive messages between servers.
- File Sharing: FTP (File Transfer Protocol) enables the transfer of files between computers by utilizing TCP/IP to manage the data packets.
These applications depend on TCP/IP communication to deliver reliable, efficient, and secure services, making it a cornerstone of modern digital interactions.
Conclusion
Understanding the TCP/IP protocol is fundamental for anyone pursuing a career in cybersecurity. It is the backbone of network communication, ensuring reliable data transfer across the internet and private networks. Mastering the TCP/IP model and its layers not only enhances your ability to troubleshoot network issues but also prepares you to secure systems effectively.
As the cybersecurity landscape continues to evolve, a strong grasp of TCP/IP communication will set you apart, helping you secure a 6-figure cybersecurity job. Dive deeper into network security and start building the skills needed for success in the tech industry.
If you’re ready to take your knowledge to the next level and learn the skills needed for a successful cybersecurity career, consider enrolling in ExcelMindCyber Institute’s 90-day program. Our comprehensive training helps aspiring professionals land 6-figure jobs in tech by teaching essential cybersecurity skills, including TCP/IP protocol and network security.
FAQ
What are the 4 types of IP addresses?
The four main types of IP addresses are:
Public IP Address: This is assigned by the Internet Service Provider (ISP) and is visible to the public internet. It allows your network to communicate with external networks.
Private IP Address: These are used within a local network (LAN) and are not routable on the internet. Common private IP ranges include 192.168.x.x, 10.x.x.x, and 172.16.x.x.
Static IP Address: This is a fixed IP address that doesn’t change over time. It’s typically used for servers or devices that need a consistent address.
Dynamic IP Address: These IP addresses are assigned by a DHCP server and can change over time. They are commonly used by home networks and devices connected to the internet.
What are the 5 TCP/IP protocols?
The five most commonly used TCP/IP protocols are:
TCP (Transmission Control Protocol): Ensures reliable data transmission by breaking data into packets and ensuring they are delivered in the correct order.
IP (Internet Protocol): Handles the addressing and routing of data packets to ensure they reach the correct destination.
FTP (File Transfer Protocol): Used for transferring files between computers over the internet.
SMTP (Simple Mail Transfer Protocol): Used for sending and receiving emails between servers.
HTTP (Hypertext Transfer Protocol): The foundation of data communication on the web, enabling the exchange of web pages between clients and servers.
What is a TCP protocol used for?
The TCP protocol is primarily used to establish a reliable, connection-oriented communication channel between two devices on a network. It breaks down large chunks of data into smaller packets, assigns sequence numbers, and ensures the packets are delivered in the correct order.
TCP also provides error-checking and guarantees the data’s integrity by requesting retransmissions if packets are lost. TCP is used for applications where reliability is crucial, such as web browsing (HTTP), email (SMTP), and file transfers (FTP).
How is TCP different from UDP?
TCP (Transmission Control Protocol) and UDP (User Datagram Protocol) are both transport layer protocols, but they differ in several ways:
TCP is connection-oriented, meaning it establishes a connection between the sender and receiver before transmitting data. It ensures reliable delivery, error checking, and the correct order of packets.
UDP is connectionless, meaning it doesn’t establish a connection before sending data and doesn’t guarantee delivery or order. This makes it faster but less reliable.
TCP is used for applications that require reliable data transfer, such as web browsing and email, while UDP is used for applications that require low-latency and can tolerate data loss, such as video streaming, online gaming, and voice calls.