Operation Per Second: Meaning, FLOPS vs IOPS 2026
Operations per second is a key metric used to measure how fast a computer system performs tasks within one second. In computing, it describes how many operations a processor, storage device, or system can complete, and it directly affects speed, performance, and responsiveness.
There are two major types of operation per second metrics. Floating-point operations per second (FLOPS) measure how fast a system handles mathematical calculations, while input/output operations per second (IOPS) measure how quickly a system reads and writes data. Both play a critical role in cybersecurity systems, where speed determines how quickly threats are detected, data is encrypted, and systems respond to attacks.
In cybersecurity, higher operations per second means faster encryption, quicker threat analysis, and more efficient handling of large volumes of sensitive data. From RSA encryption to real-time monitoring systems, performance directly impacts how secure and reliable a system is.
In this guide, you will learn what operation per second means, how FLOPS and IOPS work, how they differ from throughput, and how they apply to encryption, system performance, and cybersecurity operations.

What Is Operation Per Second in Computer Systems?
Operation per second in computer systems refers to how many tasks a system can complete within one second. These tasks can include calculations, data transfers, or processing instructions. The higher the number of operations per second, the faster and more responsive the system becomes.
In simple terms, operation per second measures performance. It tells you how quickly a computer can process information and handle workloads. This is important in cybersecurity, where systems must process large amounts of data in real time to detect threats and respond instantly.
For example, when a security system scans network traffic for suspicious activity, it performs thousands or even millions of operations per second. Each operation could involve checking patterns, analyzing behavior, or validating data. If the system has low performance, it may miss threats or respond too slowly.
An operation per second example can be seen in password verification. When a user logs in, the system processes multiple operations to verify credentials, check encryption, and grant access. A system with higher operations per second completes this process faster and more securely.
In cybersecurity environments, operation per second in computer performance directly affects:
- Threat detection speed
- Encryption and decryption processes
- System response time during attacks
- Overall system stability under heavy load
This is why engineers and security professionals rely on metrics like floating-point operations per second and IOPS to evaluate how well a system can handle real-world security demands.
Floating-Point Operations Per Second (FLOPS) Explained
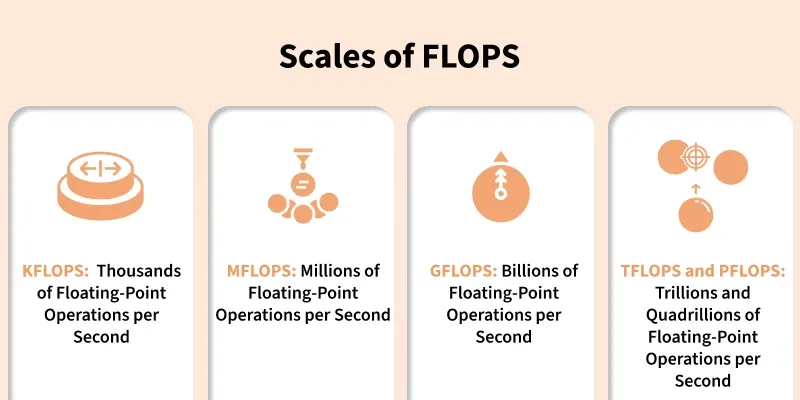
Floating-point operations per second (FLOPS) measures how many mathematical calculations a system can perform in one second. These calculations involve real numbers, including decimals, which are common in advanced computing tasks.
In computer architecture, floating point operations are handled by a special unit inside the processor called the Floating Point Unit (FPU). This unit focuses on high-precision calculations such as multiplication, division, and complex equations.
FLOPS in computer performance is especially important in areas that require heavy computation. In cybersecurity, this includes encryption algorithms, threat modeling, anomaly detection, and AI-based security systems.
To understand it simply:
- 1 FLOPS equal to one floating-point calculation per second
- 1 GFLOPS = 1 billion calculations per second
- 1 TFLOPS = 1 trillion calculations per second
The higher the FLOPS, the faster a system can process complex mathematical operations.
In cybersecurity, FLOPS plays a key role in:
- Encryption and decryption processes
- Running machine learning models for threat detection
- Analyzing large datasets for suspicious patterns
- Simulating attack scenarios to test system defenses
For example, when a system uses encryption to secure data, it performs multiple mathematical operations to convert readable data into encrypted form. These operations rely heavily on floating point operations in computer architecture. A system with higher FLOPS can perform encryption faster and handle more secure transactions at scale.
However, FLOPS alone does not determine overall system performance. It focuses only on computation speed. To fully understand system efficiency, you also need to consider how quickly data moves in and out of the system. That is where IOPS becomes important.
RELATED: What is a TCP/IP Protocol? Networking Importance in 2026
IOPS vs Throughput: What Really Matters in Cybersecurity Systems
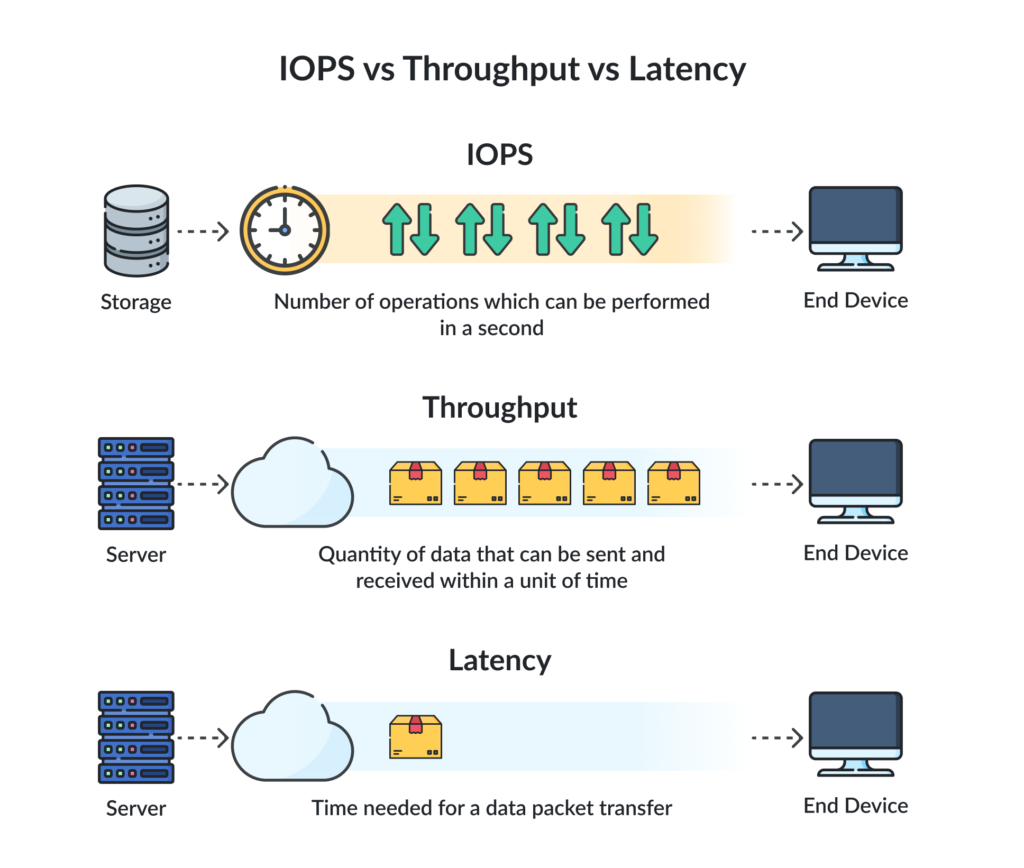
IOPS vs throughput is a critical comparison when evaluating system performance, especially in cybersecurity environments where both speed and data flow matter.
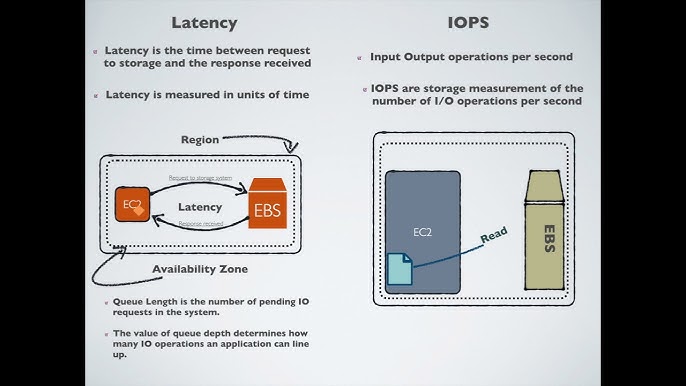
IOPS (Input/Output Operations Per Second) measures how many read and write operations a storage system can perform in one second. It focuses on how quickly a system can access and process small pieces of data.
Throughput, on the other hand, measures how much data a system can transfer in a given time, usually in megabytes or gigabytes per second. It focuses on volume rather than the number of operations.
Here is the difference in simple terms:
- IOPS = how many tasks are completed per second
- Throughput = how much data is moved per second
Both metrics are important, but they serve different purposes.
In cybersecurity systems, IOPS is crucial for:
- Real-time log analysis
- Intrusion detection systems
- Authentication processes
- Handling multiple small requests at once
For example, when a system checks thousands of login attempts, it performs many small read and write operations. High IOPS ensures these operations happen quickly without delays.
Throughput becomes important when dealing with:
- Large data transfers
- Backup and recovery systems
- Data replication across servers
However, focusing only on throughput can be misleading. A system may move large volumes of data efficiently but still struggle with handling many small operations quickly.
This is why IOPS vs throughput must be evaluated together. In cybersecurity, most real-time operations rely more on IOPS because systems constantly process small, frequent requests rather than large data transfers.
Latency also plays a role. It measures how quickly a system responds to a request. Even with high IOPS, high latency can slow down performance and affect system responsiveness.
In practice:
- High IOPS + low latency = fast and responsive system
- High throughput = efficient large data handling
To build a secure and efficient system, you need a balance of all three.
READ MORE: Why Computer Virus Prevention is Critical for Aspiring Cybersecurity Professionals
Operation Per Second Example in Cybersecurity Systems
To understand operation per second clearly, it helps to look at a real cybersecurity scenario.
Consider a login system that handles thousands of users at the same time. Every login request triggers multiple operations within a second. The system must:
- Receive the user’s input
- Check the username against a database
- Verify the password using encryption
- Validate access permissions
- Log the activity for monitoring
Each of these steps requires multiple operations per second. If the system handles 10,000 login requests at once, it may perform millions of operations in just a few seconds.
This is a simple operation per second example, but it shows how performance directly affects security and user experience.
Now take a more advanced case.
A cybersecurity monitoring system scans network traffic in real time. It performs operations such as:
- Inspecting incoming packets
- Comparing patterns against known threats
- Running anomaly detection models
- Triggering alerts for suspicious activity
All of these processes rely on high operations per second. If the system cannot keep up, it may fail to detect threats early.
Encryption is another strong example. When data is secured using encryption, the system performs repeated mathematical operations to convert readable data into a protected format. The faster these operations happen, the more efficiently the system can secure large volumes of data.
In high-security environments, systems often process:
- Millions of operations per second for monitoring
- Thousands of operations per second for authentication
- Continuous operations for encryption and decryption
A system with low performance may create delays, increase vulnerability, or fail under heavy load. On the other hand, a system with high operations per second can handle more users, detect threats faster, and maintain stability during attacks.
This is why operation per second in computer systems is not just a technical metric. It directly affects how secure, reliable, and scalable a cybersecurity system can be.
How Cryptography Uses Operations Per Second (RSA Explained)
In cybersecurity, cryptography relies heavily on operations per second to secure data. Every time a system encrypts or decrypts information, it performs multiple mathematical operations. The speed of these operations determines how fast and secure the system can handle sensitive data.
One of the most widely used encryption methods is RSA encryption.
What Is RSA Encryption?
RSA encryption is a public-key cryptographic method used to secure data during transmission. It works by using two keys:
- A public key for encryption
- A private key for decryption
When data is encrypted, the system performs complex mathematical calculations using large prime numbers. These calculations require a high number of operations per second.
How Does RSA Encryption Work?
Here is a simple breakdown of how RSA encryption works:
- The system generates two large prime numbers
- These numbers are used to create a public key and a private key
- Data is encrypted using the public key
- The encrypted data can only be decrypted using the private key
This process involves repeated modular exponentiation, which is computationally intensive. That is why systems with higher operations per second perform encryption and decryption much faster.
RSA Encryption and System Performance
In real-world systems, RSA encryption and decryption must happen quickly to avoid delays. For example:
- Secure login systems encrypt user credentials
- Web servers use encryption to protect data in transit
- Security tools verify digital signatures
Each of these actions depends on how many operations per second the system can handle.
If performance is low, encryption processes slow down. This can lead to:
- Delayed authentication
- Slower secure connections
- Reduced system efficiency
Tools Used for RSA Calculations
There are several tools used to understand and test RSA encryption processes, including:
- rsa encryption calculator
- rsa calculator
- rsa algorithm calculator
- rsa cryptosystem calculator
- rsa solver
- cryptography calculator
- rsa cryptography calculator
These tools help simulate how encryption works, but real systems perform these calculations at scale using optimized hardware and software.
RSA Keys and Security Operations
RSA encryption also depends on key generation and management. Systems perform multiple operations per second when handling keys such as:
- generate rsa key
- rsa public key
- rsa decryption
- private key encryption
- public-encrypt
- openssl decrypt private key
- decrypt password
Each of these processes requires precise and fast computation. In cybersecurity systems, faster operations per second means:
- quicker encryption and decryption
- stronger real-time security
- better handling of large volumes of encrypted data
This is why performance metrics like operation per second and FLOPS play a critical role in modern cryptographic systems.
SEE ALSO: Cloud Security Tips: How to Safeguard Your Data in 2026
What Affects Operation Per Second in Cybersecurity Systems
Several factors determine how many operations per second a system can perform. In cybersecurity, these factors directly impact how fast a system can detect threats, process data, and secure information.
Processor Architecture
The design of the CPU or GPU plays a major role in performance. Modern processors include specialized units for handling calculations and security tasks. Systems with more advanced architecture can perform more operations per second with better efficiency.
For example, processors with optimized instruction handling can process encryption and threat detection tasks faster than older designs.
Parallel Processing (Cores and Threads)
Systems with multiple cores can handle many tasks at the same time. This is known as parallel processing.
In cybersecurity:
- One core can analyze traffic
- Another can handle encryption
- Others can monitor system activity
The more cores available, the higher the total operations per second the system can achieve.
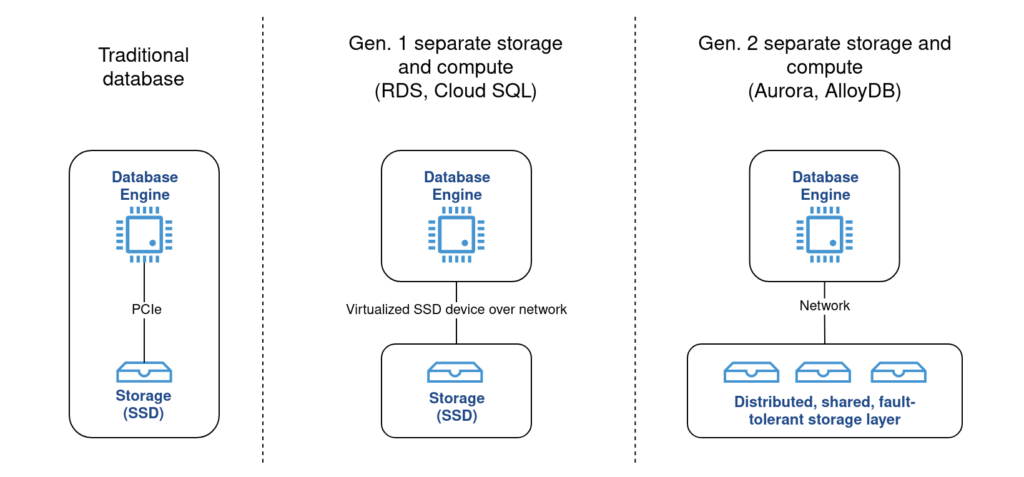
Storage Performance (IOPS Impact)
Storage speed affects how quickly data can be read and written.
Systems with high IOPS can:
- Access logs faster
- Process authentication requests quickly
- Handle multiple read and write operations without delay
Solid-state drives (SSDs) typically deliver much higher IOPS than traditional hard drives (HDDs), which improves overall system responsiveness.
Memory Bandwidth
Memory bandwidth determines how quickly data moves between the processor and memory.
If memory cannot supply data fast enough, the processor slows down, even if it has high computing power. High bandwidth ensures a steady flow of data, allowing the system to maintain high operations per second.
Algorithm Efficiency
The way software is written affects performance. Efficient algorithms require fewer operations to complete a task.
In cybersecurity, optimized algorithms can:
- Encrypt data faster
- Detect threats more efficiently
- Reduce system load
Poorly optimized code increases the number of operations required, which slows down performance.
Network Performance
Cybersecurity systems often rely on network data. If the network is slow, the system may not receive or send data quickly enough to maintain high performance.
Low latency and stable connections help systems process operations in real time, especially for monitoring and threat detection.
System Configuration and Workload
The type of workload also matters. Systems handling large volumes of small tasks need high IOPS, while systems handling large data transfers need strong throughput.
A system that is not properly configured for its workload may struggle, even if it has powerful hardware.
In cybersecurity, operation per second is not controlled by a single factor. It is the result of how well hardware, software, and system design work together. Improving any of these areas can increase performance, but the best results come from optimizing all of them together.
MORE: Is a Masters in Cybersecurity Worth It in 2026?
Why Operation Per Second Matters More Than You Think
Operation per second is not just a technical metric. It directly affects how well a cybersecurity system performs in real-world situations.
When systems process more operations per second, they respond faster. This speed matters in security environments where delays can lead to serious risks.
Faster Threat Detection
Cybersecurity systems constantly analyze data to identify threats. They scan logs, inspect network traffic, and compare patterns against known attacks.
A system with higher operations per second can:
- Detect threats earlier
- Analyze more data in real time
- Reduce the chance of missed attacks
Stronger Encryption Performance
Encryption depends on repeated calculations. Systems perform multiple operations per second to secure data and protect communication.
Higher performance allows systems to:
- Encrypt data faster
- Decrypt information without delay
- Maintain secure connections under heavy load
This is especially important for systems using methods like RSA encryption, where mathematical operations are intensive.
Better System Stability Under Load
Cybersecurity systems often handle spikes in activity. This can happen during:
- Large-scale login attempts
- Distributed attacks
- High network traffic
If the system cannot handle enough operations per second, it may slow down or fail.
High-performance systems remain stable even when demand increases.
Improved User Experience
Security should not slow down users. Systems with high operations per second can:
- Process logins quickly
- Verify credentials instantly
- Reduce waiting time
This creates a smoother and more secure experience.
Real-Time Response to Attacks
In cybersecurity, response time is critical. Systems must react immediately when a threat is detected.
Higher operations per second enables:
- Instant alerts
- Automated threat response
- Faster containment of attacks
Operation per second affects every part of a cybersecurity system. From detection to response, higher performance leads to better security, reliability, and efficiency.
Common Mistakes When Evaluating Performance
Many people misunderstand how to measure system performance. They focus on one metric and ignore others, which leads to poor decisions and weak system design.
Focusing Only on FLOPS
FLOPS in computer performance measures calculation speed, but it does not tell the full story.
A system may have high floating-point operations per second and still perform poorly if it cannot handle data efficiently. Cybersecurity systems rely on both computation and data access, so focusing only on FLOPS can be misleading.
Ignoring IOPS
Some systems handle calculations well but struggle with data access. This happens when IOPS is low.
In cybersecurity, systems constantly read and write data. Low IOPS can slow down:
- Log analysis
- Authentication processes
- Threat detection systems
Even with strong processing power, poor storage performance can create bottlenecks.
Overlooking Latency
Latency measures how quickly a system responds to a request.
A system may have high operations per second but still feel slow if latency is high. This delay can affect:
- Login systems
- Real-time monitoring
- Security alerts
Low latency is just as important as high performance.
Confusing Throughput with Speed
Throughput measures how much data moves at once, not how fast individual operations are completed.
A system with high throughput may still struggle with handling many small tasks. This is why IOPS vs throughput must be evaluated correctly.
Ignoring Real-World Workloads
Performance metrics mean little without context.
A system designed for large data transfers may not perform well in environments that require rapid, small operations. Cybersecurity systems often fall into the second category.
Always evaluate performance based on actual use cases.
Assuming Higher Numbers Always Mean Better Performance
Higher values do not always translate to better results.
For example:
- High FLOPS without good memory support can slow down processing
- High IOPS without proper system optimization can still cause delays
Performance depends on how well all components work together.
Understanding these mistakes helps you evaluate systems more accurately. In cybersecurity, balanced performance is more important than chasing a single high metric.
Conclusion
Operation per second is a core metric that defines how fast a system can perform tasks within a second. In cybersecurity, this speed is not just about performance. It directly affects how quickly systems detect threats, process data, and secure sensitive information.
Floating-point operations per second focuses on computational power, while IOPS measures how efficiently systems handle data access. Together, they provide a clearer picture of how a system performs under real-world conditions. When combined with factors like latency and throughput, they help you understand whether a system can handle modern security demands.
From encryption processes like RSA encryption to real-time threat monitoring, every cybersecurity function depends on how many operations per second a system can manage. Higher performance allows faster encryption, quicker responses, and better stability under pressure.
The key is balance. Strong cybersecurity systems do not rely on a single metric. They combine processing power, storage performance, and efficient system design to handle both computation and data flow effectively.
When you understand operation per second in computer systems, you move beyond basic performance metrics. You begin to see how speed, security, and reliability work together to protect systems in real time.
give me cta better than the following: If you’re ready to take your knowledge to the next level and learn the skills needed for a successful cybersecurity career, consider enrolling in ExcelMindCyber Institute’s 90-day program. Our comprehensive training helps aspiring professionals land 6-figure jobs in tech by teaching essential cybersecurity skills, including TCP/IP protocol and network security.
If you want to turn this knowledge into real income, the next step is simple.
Join ExcelMindCyber Institute’s 90-day program and learn how to apply these concepts in real-world cybersecurity roles. You won’t just study theory. You’ll work on practical projects, build experience, and position yourself for high-paying roles in GRC and security operations.
If you’re serious about breaking into cybersecurity and earning at a higher level, this is where you start.
FAQ
How do you calculate FLOPS?
FLOPS is calculated by multiplying the number of operations a processor can perform per cycle by its clock speed (in cycles per second), and then by the number of cores.
A simplified formula looks like this:
FLOPS = Operations per cycle × Clock speed × Number of cores
For GPUs, manufacturers usually provide the FLOPS value directly because it depends on architecture-specific factors like parallel cores and instruction sets.
Is 70 trillion operations per second good?
Yes, 70 trillion operations per second (70 TFLOPS) is considered very high performance.
This level of performance is suitable for:
Advanced AI workloads
High-end cybersecurity simulations
Real-time data processing at scale
For context, most everyday systems operate far below this range, so 70 TFLOPS is typically found in high-performance GPUs and enterprise-grade systems.
What makes the CPU faster?
Several factors determine CPU speed and performance:
Clock speed (higher GHz means faster cycles)
Number of cores (more cores allow parallel processing)
Cache size (faster data access)
Architecture efficiency (how well instructions are handled per cycle)
Thermal management (prevents throttling under load)
In cybersecurity, faster CPUs improve encryption, threat detection, and real-time processing.
How many FLOPS is RTX 4090?
The NVIDIA GeForce RTX 4090 delivers around 82.6 TFLOPS of single-precision (FP32) performance.
This makes it one of the most powerful consumer GPUs available, capable of handling:
AI model training
High-speed encryption workloads
Advanced simulations
Its high FLOPS comes from thousands of parallel cores working together, which significantly boosts operations per second compared to traditional CPUs.